Apple, one of the largest tech companies around, is no stranger to criticism. Arguably, this very characteristic propelled them to such lofty heights in the first place. Charismatic figures like Steve Jobs became well-known for their positive response to customer feedback. Thus, with each iteration of products becoming more user-friendly than the next.
However, one area where Apple has certainly struggled is user privacy and security. Although lapses in security might seem common, the exact scale of people affected by their Apple devices remains huge.
One moral grey area of hacking and exploiting Apple’s security was always the concept of ‘jailbreaking‘. This usually illegal but generally harmless practice involved users hacking through the iPhone’s security to access root control. The aim of this? To obtain apps, files, and features typically locked away behind the App Store’s paywall.
Apple long opposed this practice as violating their user agreement and terms of service, but every year the exploits remained easy. However, a recent finding by security firm IronPeak about Apple’s proprietary T2 security chipset may leave Macs worldwide at risk.
Hackers have discovered how to get into Macbook laptops using the same principles of jailbreaking
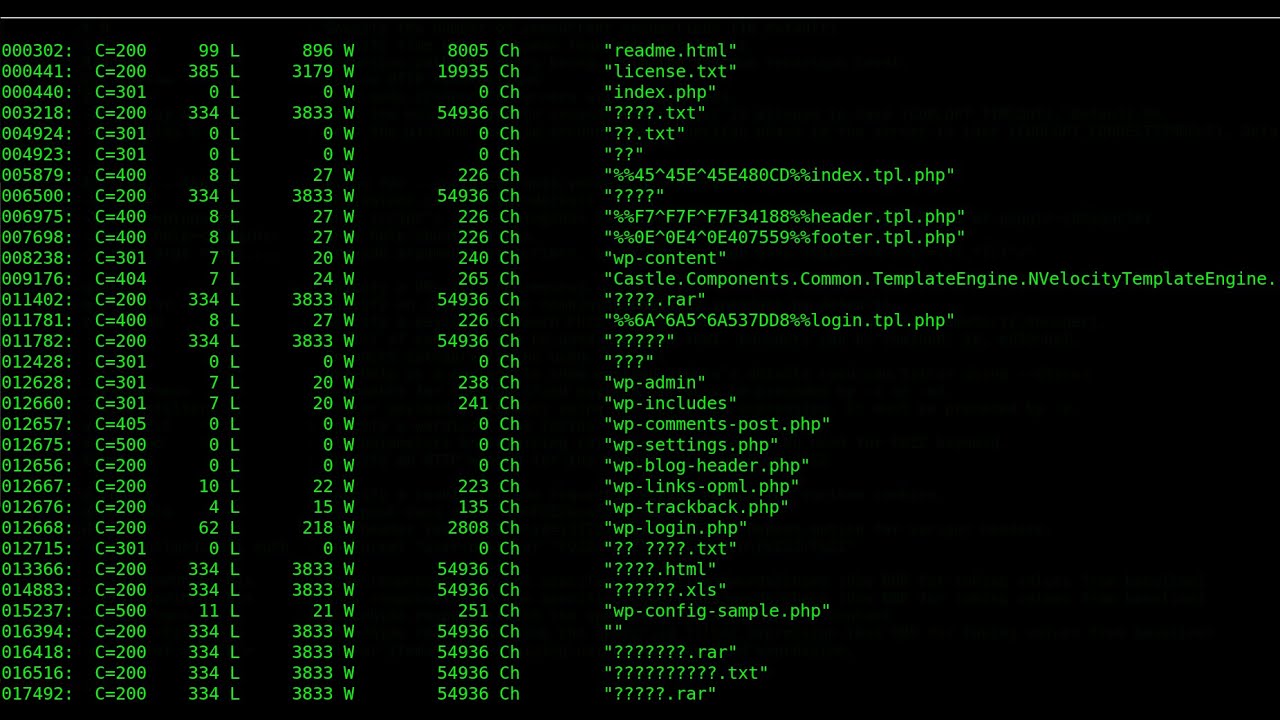
the initial series of jailbreaking generally relied on two hacking tools. These were informally called ‘Blackbird‘ and ‘Checkm8‘ by users involved in their invention. These two tools can let users overcome firewalls, gain control of the root directory, kernel and bypass the FileVault2 encryption. All that’s required? A simple, easily available debugging cable to use Checkm8 through. And to prevent the T2 chipset from ending the hack in fatal error, Blackbird overrides the decryption command. Thus, the user can circumvent both security measures and access the SEP (Secure Enclave Processor). That might sound like a bunch of nerdy jargon, but it means that all of your data is now compromised.
By installing a keylogger at the firmware level, the hacker gains options. They can either choose to then quickly transfer the desired data and leave. Or, even more alarmingly they can then leave the keylogger in to remotely access it later. That means that a hacked device can transmit personal data at any point, the owner unaware. Either way, the issue is not something that Apple can easily resolve, for a few reasons.
Because the exploit is rooted in the hardware itself, Apple cannot patch it out without a complete recall of products
As several security experts note, it seems unlikely Apple can do anything about existing devices. The problem comes from their Macbook’s OS, at the hardware level. Unfortunately, the only way to fix this would involve new hardware. That means either Apple replaces every post-2018 MacBook in the world, or fixes the T2 chip for later versions. The OS in question, with its glaring security hole, is the same as that on the iPhone A10 SoC. This means the basic problems carry over.
This entire vulnerability comes from a single opening in coding. The T2 debugging access interface, which normally comes sealed off, is completely ajar. So, potentially every MacBook since 2018 (when this particular chipset released) may come at a risk.
IronPeak warns that laptops handed over to authorities or left unattended may carry the most risk
The only way a hacker can compromise a Mac is by physically accessing it. Even then, they would need several minutes or longer to pull off the hack. So, the biggest window a hacker would have arrives when the owner leaves their device free. Even if its is for a security checkpost, caution is advised.
For more on the state of Apple, MacBooks and chips, stay tuned!