Yesterday was the 14th anniversary of the launch of Twitter, a social media platform we’ve all come to know and love. However, on a day that was supposed to be about the celebration for Twitter, disaster struck.
In what will quite possibly go down as one of the worst cyberattacks that the website has ever witnessed, the entire Twitter community was compelled to evaluate and think deeper about how much do we actually rely on these websites that can be torn apart just like that, in a snap.
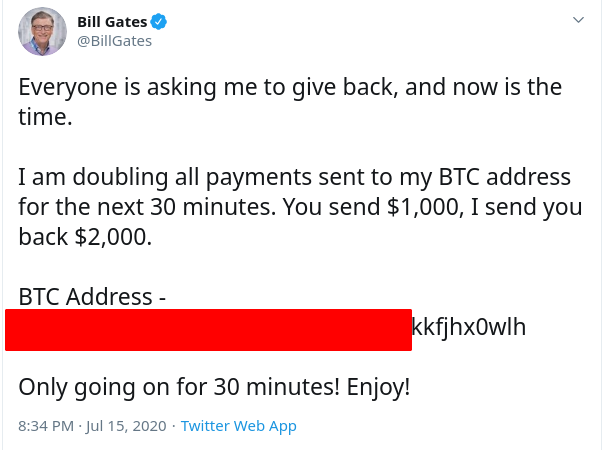
If you still don’t know what happened, here’s a brief summary for you. Basically, some verified Twitter accounts of celebrities started Tweeting some rather unusual things yesterday. It seemed like a promotional campaign to the naive eye but was obviously something far more treacherous.
Verified accounts like Elon Musk, Bill Gates, Mr. Beast, and even Apple among many others tweeted out that they were doing a “giveaway”. The giveaway was essentially the oldest scam trick in the book. It required you to send some Bitcoins to a wallet address and get twice the amount in return.
While the scam is pretty obvious and we’ve seen this countless times before, a lot of people actually fell for it just because many verified celebrities were tweeting this. This also plays into the entire celebrity ‘worship’ culture that’s present on Twitter as people would believe anything that someone with the influence of Bill Gates or Elon Musk would say.
The Hackers made over $120,000 in a span of 2 hours
While the majority of people didn’t fall for the very obvious scam, a lot of people still did. As soon as the tweets rolled out, people started frantically sending Bitcoins to their favorite celebrities in hopes of getting double returns. However, some eagle-eyed users on Twitter noticed that the BTC wallet address that the hackers were using was actually the same across all verified accounts.
People were sending BTC to a single account, and obviously, looking into the transactions of a single account is much easier. So, in total, the hackers managed to make over $100,000 in BTC using only a single wallet, which is somewhat mind-boggling. And, while they did change the address to another wallet later, Twitter obviously didn’t let this go on for very long and brought down its hammer.
The hacker(s) shared a single wallet on all of the hacked accounts! pic.twitter.com/0ZlIW8zcXj
— Aleph א (@no_itsmyturn) July 15, 2020
In the end, the hackers managed to scam over $120,000 out of people. What did Twitter do? Well, for the first two hours, it seemed like the platform was helpless as if they’d been held hostage by the hackers.
Also read: The Anonymous Twitter account might be fake
Eventually, though, Twitter stopped all verified accounts from tweeting and that resulted in a strange landscape without any verified account being able to say anything. This meant that the entire media and other verified accounts were unable to tweet, which felt quite bizarre and jarring considering how much information is being poured and posted onto Twitter every second.
How did the hackers gain access to all the Verified Twitter accounts?
I don’t remember the last time something like this happened on a social media platform, on such a massive scale. The most puzzling part of the entire thing is the fact that the hackers managed to gain access to so many verified accounts, all in one go.
According to Twitter, the hackers orchestrated the “social engineering attack” by targeting some of the website’s employees who had access to internal tools and systems. So, the hackers were able to gain access to the verified accounts via Twitter employees and managed to tweet on their behalf.
We know they used this access to take control of many highly-visible (including verified) accounts and Tweet on their behalf. We’re looking into what other malicious activity they may have conducted or information they may have accessed and will share more here as we have it.
— Support (@Support) July 16, 2020
While this does seem like a plausible explanation for what happened, one does have to ask why do the Twitter employees have such access? Why are they able to send out tweets from verified accounts? Isn’t that too much of a security risk and shouldn’t their access be limited to moderation only?
And, even though the investigation is still going on and further details are yet to be revealed, this calls for a serious rethinking on Twitter’s part. The platform has to be more vigilant and diligent in the future. Not only that, but we also need to hold these platforms accountable as well because something like this is just too dicey in the modern age.
We also need to reflect on how much we rely on Social Media platforms
Of course, such an incredible lapse of security holds threats that we cannot even fathom. I mean, it is a miracle that the hackers only used the verified accounts to get some cash and not for other nefarious means that could have resulted in some very grave real-world disasters.
Over the years, Twitter has gained some good karma over their philosophies about how politics are handled on the platform. In addition to that, the security of the website has not really been that much of a major issue either with most people preferring Twitter to the likes of Facebook.
Also read: Social Media and our grave ‘Black Mirror’ reality
Having said that, we also need to re-evaluate ourselves. The amount of information that we dump on social media every day is obviously concerning and this has been an age-old debate. And, while we cannot just shut everything down and go back to caveman days, we need to make sure that these platforms are secure for us.
This starts with personal caution and then extends to the platform itself. We need to decrease our reliance on social media and the information that comes with it. For instance, believing everything that we see on the internet has been an incredibly damaging thing to society as a whole, especially in such a tumultuous global political environment.
In addition to that, the fact that literally all of your social media activity, information, and your account can be taken over in a snap is just a scary reality that we need to counter. People have hacked social media platforms before and they are going to do it again.
We just need to ask ourselves a couple of questions. When are we going to stop the trend of sporadic concern and outrage and instead focus on coming up with a long-term solution and defensive mechanism against the next inevitable attack?